LayerZero Ends Single-DVN Support After $290M Kelp Exploit
LayerZero says it will no longer sign messages for applications still using a 1-of-1 decentralized verifier network (DVN) setup after the roughly $290 million Kelp DAO rsETH bridge exploit on April 18.
What LayerZero says happened
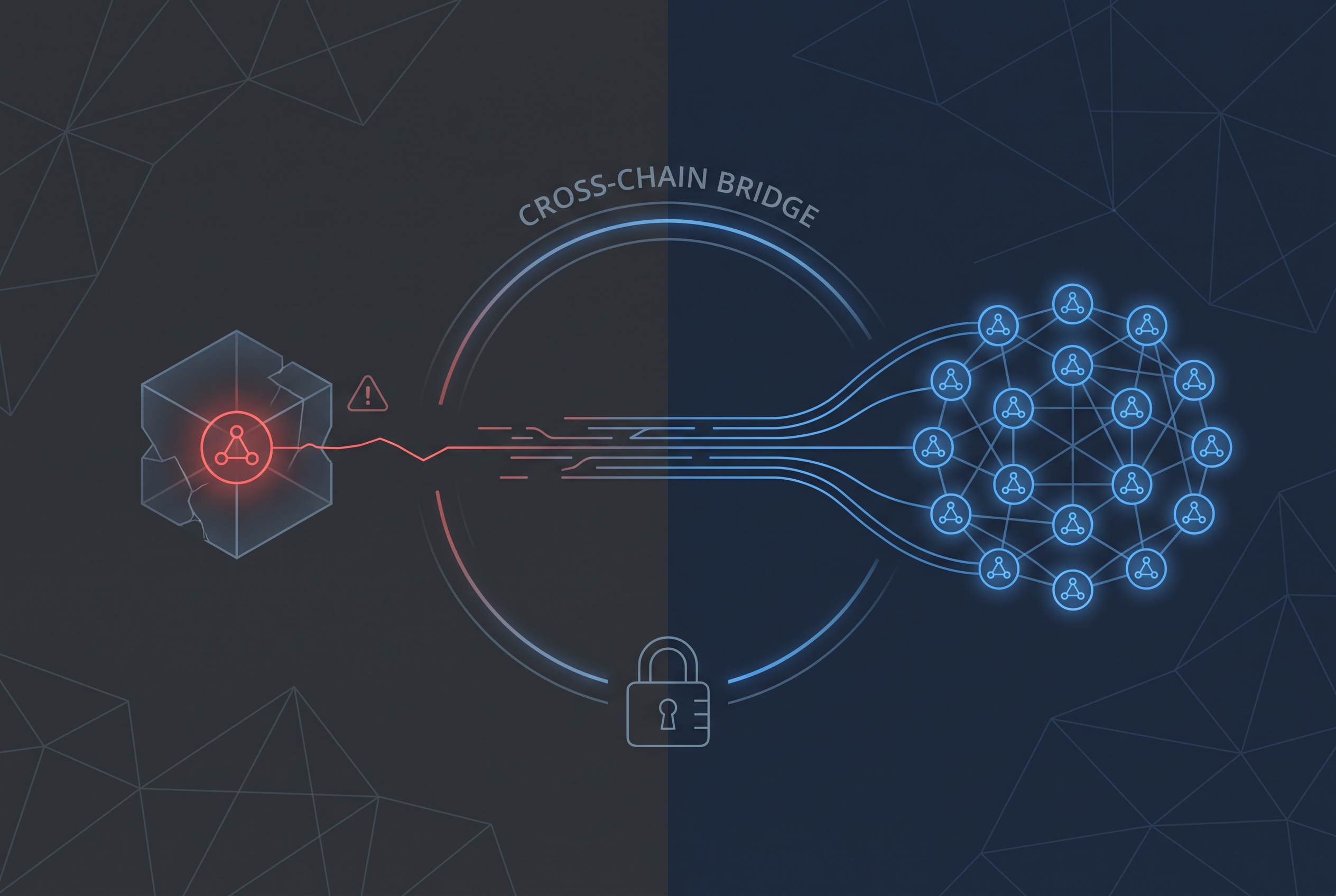
In its incident statement, LayerZero said the attack did not exploit the core protocol itself. Instead, it said attackers likely linked to North Korea's Lazarus Group, specifically TraderTraitor, poisoned RPC infrastructure used by the LayerZero Labs DVN and then used a DDoS attack to force traffic onto the compromised nodes.
LayerZero said the forged message only succeeded because Kelp's rsETH bridge relied on a single verifier, leaving no second DVN to reject a bad cross-chain message. The company said it is now contacting apps that still run 1/1 configurations and will require migration to multi-DVN setups with redundancy.
Why this matters
That policy shift matters beyond Kelp. LayerZero's own integration checklist already warns teams to configure DVNs explicitly instead of depending on defaults, and the company is now turning that guidance into an operational requirement.
Responsibility is still disputed. CoinDesk reported that Kelp plans to argue the criticized setup reflected LayerZero's onboarding defaults and documentation, not an unusual configuration Kelp invented on its own. So the conservative takeaway is narrower than the finger-pointing: the exploit has pushed one of crypto's major cross-chain providers to harden its minimum security baseline for integrators.